Security teams rarely migrate a SIEM because everything is working perfectly.
Most QRadar estates that reach the point of review show the same signs. Log ingestion has grown beyond original estimates. Licensing feels tight. Use case performance varies depending on which parts of the environment are talking. Analysts rely on workarounds more than they admit. None of this means QRadar is broken. It means the organisation has changed.
The conversation around a QRADAR to Elastic SIEM migration checklist usually starts with tooling. It should start with exposure.
Elastic brings flexibility. It also removes some guardrails. That combination works well for mature teams and creates friction for others. The difference lies in preparation, not technology.
Before planning dashboards or recreating rules, it is worth pausing to examine what is actually being moved.
Why Organisations Consider Elastic
IBM QRadar has been a stable platform for many years. Its correlation engine is predictable. Offence management is structured. Many SOC teams know it well.
Elastic Security, built on the Elastic Stack, offers a different model. Search is fast. Data handling is more fluid. Scaling patterns look different. Licensing mechanics change the cost discussion.
The shift is not purely financial. Some teams want tighter integration with cloud workloads. Others want to reduce dependency on proprietary data models. In some cases, the decision follows a broader move toward cloud-native tooling.
None of these drivers guarantee success. A rushed migration tends to surface hidden dependencies that were never documented.
Start With Data, Not Features
Every SIEM migration exposes a simple truth: data quality determines everything.
QRadar environments often accumulate legacy log sources. Some are redundant. Others have parsing exceptions quietly sitting in custom DSMs. When moving to Elastic, these inconsistencies do not disappear. They become visible.
Mapping log sources to Elastic integrations takes effort. Normalisation must be deliberate. Teams that assume “logs are logs” often discover field mismatches weeks into testing.
It helps to categorise log sources by value:
- High-risk systems tied to crown-jewel assets
- Detection-critical telemetry such as EDR and identity logs
- Compliance-only feeds that rarely trigger investigations
- Legacy feeds nobody has validated in years
The temptation is to migrate everything. A more disciplined approach questions whether everything deserves to move.
Elastic’s schema flexibility makes ingestion easy. Detection logic, however, depends on structure. A careless ingest phase leads to brittle rules later.
Detection Logic Rarely Ports Cleanly
QRadar rules often evolve over years. They combine reference sets, flow data, and event correlations in ways that are hard to replicate exactly.
Elastic uses a different detection model. KQL queries, threshold rules, and machine learning jobs replace QRadar’s rule wizard logic. Rewriting detections is not a copy and paste exercise. It is closer to re-engineering.
Teams should record:
- Offences triggered in the last twelve months
- Rules tied to regulatory controls
- Custom correlations built to cover environment-specific risks
- Rules that never trigger but still consume resources
A migration presents an opportunity to simplify. Some legacy rules can retire quietly. Others need redesign.
Blind replication leads to clutter in the new platform.
The Practical QRADAR to Elastic SIEM Migration Checklist
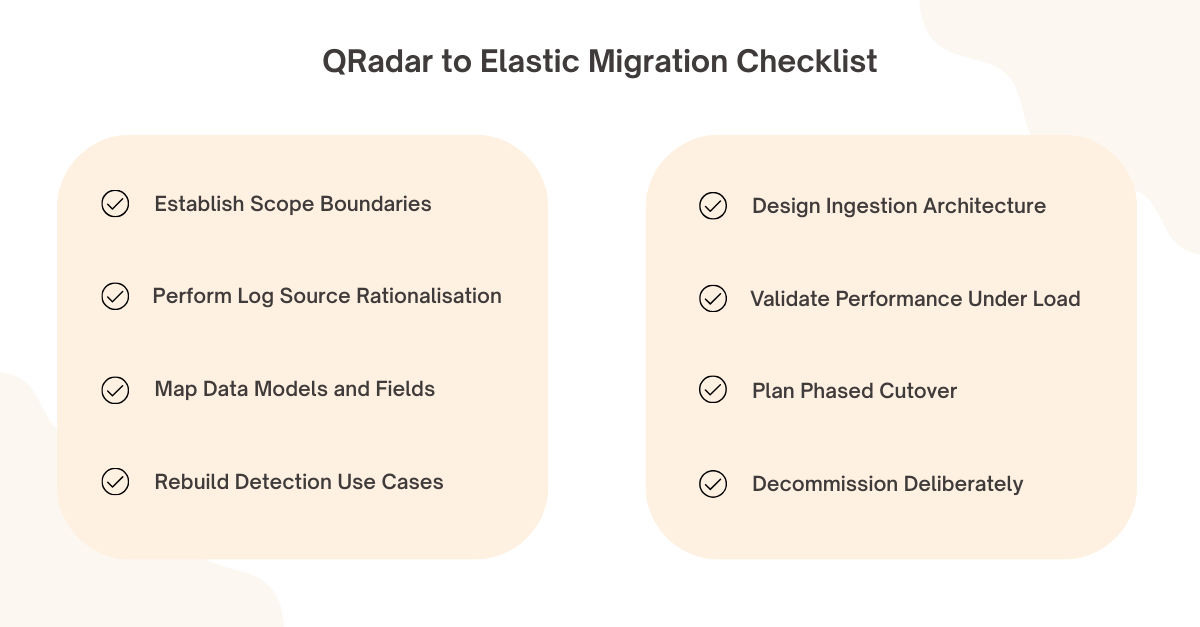
Before diving into the steps, it helps to visualise the journey as a controlled sequence rather than a technical swap. Each stage builds on the previous one. Skipping ahead tends to create rework.
Establish Scope Boundaries
Define which business units, log sources and integrations are in scope. Lock the scope early. Scope drift during migration creates chaos.
Perform Log Source Rationalisation
Catalogue every active and inactive source in QRadar. Remove redundant feeds before designing Elastic ingestion pipelines.
Map Data Models and Fields
Compare QRadar event properties with Elastic Common Schema. Identify gaps and required field transformations.
Rebuild Detection Use Cases
Translate priority rules into Elastic detection logic. Validate them using historical data where possible.
Design Ingestion Architecture
Decide between Elastic Agent, Beats, or other collection methods. Consider network segmentation and data routing.
Validate Performance Under Load
Simulate realistic event rates. Watch query latency and rule execution times. Performance surprises usually appear here.
Plan Phased Cutover
Avoid a big-bang switch. Run both platforms in parallel long enough to validate detection coverage.
Decommission Deliberately
Archive QRadar data according to retention requirements. Remove collectors only after verification.
Each of these steps sounds straightforward on paper. In practice, the friction sits in the detail. Field mapping takes longer than expected. Historical data tests uncover edge cases. Analysts resist workflow changes.
None of that indicates failure. It reflects the depth of dependency a SIEM creates.
Analyst Workflow Matters More Than Dashboards
SOC teams grow accustomed to certain flows. QRadar offences follow a defined lifecycle. Elastic cases look and behave differently.
Training should focus less on navigation and more on investigative logic. Elastic’s search capability can accelerate investigations, but only if analysts know how to structure queries properly.
Migration fatigue often shows up as frustration in the SOC. Alert noise feels different. Triage screens change. Short dips in productivity are normal. Ignoring that human impact creates longer-term resistance.
A pilot group helps. Let a subset of analysts operate in Elastic first. Capture feedback. Adjust rule tuning before full rollout.
Integration With EDR and Identity Systems
Modern detection relies heavily on endpoint and identity telemetry. Elastic integrates well with several EDR platforms, but integration quality depends on configuration discipline.
Where organisations use CrowdStrike Falcon, telemetry ingestion must preserve critical context fields. Identity platforms require careful parsing to avoid blind spots in authentication monitoring.
The goal is not simply to see alerts in Elastic. The goal is to correlate them meaningfully with network, cloud, and user activity.
SIEM migrations fail quietly when integrations appear functional but lack usable context.
Performance, Storage And Cost Realism
Elastic offers flexibility in storage tiers and scaling models. That flexibility demands forecasting discipline.
Event growth rarely stabilises. Cloud workloads generate variable volumes. Retention policies often expand under regulatory pressure.
Modelling storage needs for one year is optimistic. Modelling for three years forces more honest conversations.
Cost comparisons between QRadar and Elastic should include infrastructure, operational overhead, and staff capability. Licence cost alone distorts the picture.
Elastic’s strength lies in scalability. Without governance, that strength turns into uncontrolled growth.
Compliance and Audit Continuity
Compliance teams expect continuity. Reporting formats may change during migration. Audit trails must remain intact.
Historical QRadar data cannot simply vanish. Retention obligations vary by sector. Some organisations maintain read-only QRadar access for a defined period post migration.
Auditors rarely object to platform changes. They object to gaps in evidence.
Clear documentation of the migration plan, detection coverage mapping, and validation testing reassures stakeholders.
Governance During Transition
Migrations attract side projects. Someone suggests adding new log sources mid-stream. Another team proposes redesigning alert taxonomy.
Governance prevents drift. A small steering group with authority to accept or reject changes helps maintain focus.
Elastic’s openness encourages experimentation. During migration, experimentation should stay controlled.
Once stability returns, innovation can resume.
Conclusion
A QRADAR to Elastic SIEM migration checklist is useful only if it reflects operational reality. Technology differences matter. Human and process dependencies matter more.
Elastic can provide flexibility, scalability, and strong search capability when implemented with discipline. QRadar’s structured approach may still suit certain environments. The decision should reflect risk appetite, internal skill depth and long-term architectural direction.
CyberNX can help you make the decision based on practical exposure across both platforms. They can help you design and implement Elastic SIEM according to best practices on Elastic Cloud, on-premises, or public cloud to meet your business requirements.
Migration is rarely about replacing software. It is about reshaping how detection and response operate day to day. When handled with care, the shift becomes an opportunity to simplify and strengthen rather than disrupt.